ASM vs. CTEM Explained: Two Sides of the Same Security Coin
In recent years, the terms Attack Surface Management (ASM) and Continuous Threat Exposure Management (CTEM) have become staples in security conversations. Both promise to help organizations understand and reduce risk across an ever-expanding digital footprint.
Yet while ASM and CTEM sound related—and often overlap—they’re not interchangeable. Confusing the two can leave critical gaps in your security posture or lead to wasted investments.
Let’s unpack what each approach really means, where they intersect, how they differ, and how to decide which (or both) your organization truly needs.
Understanding Attack Surface Management (ASM)
Attack Surface Management emerged as a response to the exploding number of external assets organizations own—many of them unknown, unmonitored, or forgotten.
In essence, ASM is about visibility. Its core mission is to answer one deceptively simple question:
“What do we actually have exposed to the internet?”
ASM solutions continuously scan and map an organization’s external attack surface: domains, subdomains, IPs, cloud instances, APIs, and web applications. They identify shadow IT, misconfigurations, and forgotten assets that could serve as entry points for attackers.
Key capabilities of ASM include:
- Discovery: Uncovering every internet-facing asset—known and unknown.
- Classification: Grouping and contextualizing assets by business unit, owner, or risk category.
- Assessment: Highlighting vulnerabilities, misconfigurations, or policy violations.
- Monitoring: Keeping an eye on changes and new exposures over time.
Where ASM Shines
ASM provides foundational visibility—a digital inventory that security teams can’t operate without. For organizations starting their external risk journey, ASM delivers immediate value: it helps you understand your footprint, identify unknowns, and prioritize hygiene.
But visibility is not the same as validation. And that’s where the limitations begin.
The Limitations of ASM
ASM tells you what’s exposed, not necessarily what’s exploitable.
By its nature, ASM produces a high volume of findings—many of which are low-impact or false positives. For example, an open port or outdated library may look risky but might not be exploitable in practice. Without context, security teams often end up chasing ghosts—reviewing and remediating issues that don’t actually impact the risk posture.
In other words, ASM helps discover the “surface”, but it doesn’t tell you which exposures matter most right now. As environments grow and change daily, this static visibility model struggles to keep pace with the dynamic nature of real-world threats.
That’s where CTEM steps in.
What Is Continuous Threat Exposure Management (CTEM)?
Gartner introduced the CTEM framework in 2022 as an evolution of ASM—bridging the gap between visibility and actionable validation.
CTEM is a strategic, end-to-end program that helps organizations continuously assess and validate how exploitable they truly are, from the attacker’s perspective.
Think of it as moving from “finding assets” to “proving exposures.”
CTEM follows a continuous five-stage cycle:
- Scoping: Define what to evaluate (assets, business processes, attack paths).
- Discovery: Identify exposures across internal and external environments.
- Prioritization: Rank exposures by exploitability, impact, and business context.
- Validation: Confirm whether exposures can be successfully exploited in practice.
- Mobilization: Feed validated insights into remediation workflows and strategic decisions.
Why CTEM Is Transformative
CTEM aligns security visibility with business reality. Instead of endless lists of “potential risks,” organizations get a validated understanding of what attackers could actually exploit right now.
That means better prioritization, fewer wasted cycles, and faster measurable risk reduction.
Where ASM provides the “map,” CTEM provides the GPS with live traffic—showing not only where you are but how to reach your destination safely.
ASM vs. CTEM: The Key Differences
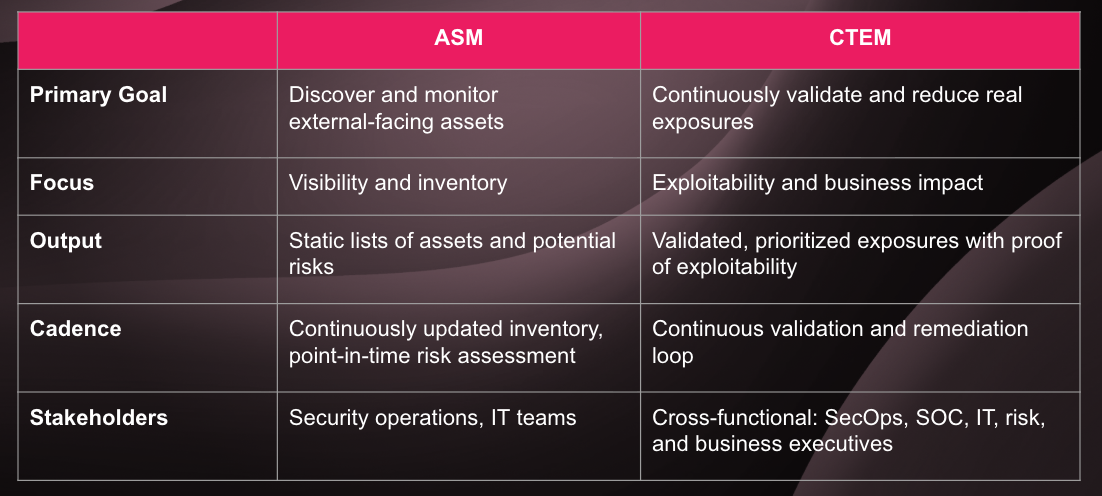
In short, ASM is about knowing what’s out there. CTEM is about knowing what matters most.
When Do You Need Each?
Start with ASM if:
- You lack visibility into your digital footprint.
- You suspect shadow IT or unmanaged assets.
- Your attack surface changes frequently due to M&A, cloud growth, or third-party integrations.
ASM gives you a crucial foundation—a single source of truth about what’s exposed to the internet. But don’t stop there.
Adopt CTEM when:
- You already have decent asset visibility but need to understand real risk.
- You’re overwhelmed by false positives and want proof of exploitability.
- You need to align technical risk with business priorities.
- You want to continuously demonstrate measurable exposure reduction to executives or the board.
In practice, many organizations run ASM as the input layer to a CTEM program. ASM discovers; CTEM validates and operationalizes.
The Future of Exposure Management
The security landscape is shifting from detection to validation.
Attackers don’t care how many vulnerabilities you know about—they care about the ones they can exploit. Security leaders are realizing that evidence, not assumptions, must drive prioritization and decision-making.
ASM will continue to play an important role in digital risk discovery. But without CTEM’s validation and mobilization layers, it remains a visibility tool—helpful, but incomplete.
In fact, in many practical implementations, CTEM can effectively replace standalone ASM solutions. Because CTEM inherently includes continuous discovery of external assets as part of its lifecycle, it already delivers ASM’s visibility layer—then goes further by validating exposures, prioritizing by exploitability, and driving remediation.
Organizations that adopt a CTEM mindset move beyond passive monitoring toward proactive, measurable risk reduction. They know what’s real, act faster, and focus resources where it truly matters.
Conclusion
ASM and CTEM are not competing paradigms—they’re part of the same evolution.
If you already have an ASM solution, CTEM can replace it with a more comprehensive approach that not only discovers assets but validates and prioritizes real exposures across them.
And if you don’t yet have either, starting with CTEM gives you everything ASM offers—and much more.
Want to learn more about CTEM?
Discover how modern security teams are validating exposures, cutting false positives, and focusing on what’s real.





